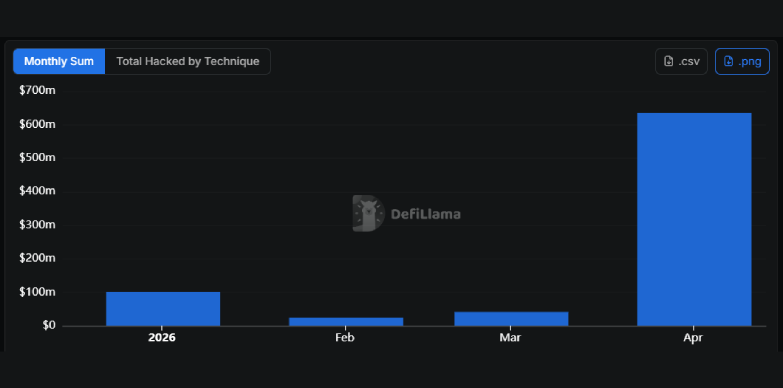
- In the past four months, cryptocurrency exploits have exceeded $770 million according to DeFiLlama.
- Drift and KelpDAO were the two largest hacks and accounted for approximately 76% of cryptocurrency exploit losses in 2026.
- AI-powered cryptocurrency exploits remain speculative, but the risks of automation are growing.
The cryptocurrency industry is currently facing its most worrying security period yet. By April 2026, according to data provided by DeFiLlamaMore than $770 million has already been stolen through cryptocurrency-related exploits, and interestingly, nearly 76% of those losses have been linked to North Korea’s cyber operations.
While major incidents such as the Drift Protocol and KelpDAO exploits have accounted for most of the value stolen, the sheer pace of attacks and increasing sophistication of cryptocurrency exploitation methods is raising questions about security in the DeFi space.
Much of the damage incurred during the year came from several major accidents. The two largest publicly reported cryptocurrency exploits were Drift protocol and KilbdawTogether, they represent more than $577 million in stolen assets. Drift reportedly lost approximately $285 million, while the value of the KelpDAO exploit was estimated at approximately $292 million.
The Drift Protocol exploit occurred on April 1, and the attackers reportedly used social engineering to gain trust over time, then manipulated governance approvals to whitelist fake collateral. This allowed them to deposit worthless assets and borrow real money such as USDC, ETH, and SOL.
In the case of KelpDAO, attackers exploited a vulnerability in the bridge verification that allowed them to open unsupported rsETH. They then used those stolen collateral via DeFi lending platforms to borrow hundreds of millions in legitimate assets.
Together, these two attacks accounted for nearly 76% of all cryptocurrency losses recorded in 2026 through April.
The DeFi security model is facing increasing pressures beyond smart contract bugs
The Drift and KelpDAO attacks exposed vulnerabilities in DeFi that went beyond simple programming flaws. The Drift exploit highlighted how governance systems, multi-signature security, and operational processes can be exploited when protocols rely on signer trust without adequate safeguards such as time locks or more stringent transaction validation.
KelpDAO demonstrated the risks of bridge infrastructure built on single verification models, where a compromised verification layer can lead to such huge losses.
Such incidents could lead to increased regulatory scrutiny around DeFi governance, bridge security and cross-chain infrastructure, as billions are pumped into the DeFi space. Regulators may push for more stringent operational standards, while protocols may face pressure to adopt stronger security frameworks.
The broader impact on the ecosystem can be significant. Repeated, large-scale hacks could weaken investor confidence, increase security premiums, and shift liquidity toward protocols with stronger governance and infrastructure protection. Ultimately, the future of DeFi may increasingly depend on redesigning governance systems, bridge architecture, and operational defenses to withstand human and machine-assisted attackers.
Aside from major incidents, many smaller attacks have also occurred. Platforms like Wasabi Protocol ($5.5 million), Aftermath perps ($1.14 million), Grinex ($15 million), Resolv Labs ($24.5 million), and many other bridge or liquidity systems, have seen security failures ranging from compromises of private keys to tampering with smart contracts.
These two attacks alone dramatically reshaped this year’s total losses and reinforced how a small number of highly successful breaches can dominate cryptocurrency security metrics. Moreover, according to TRM Laboratories report And multiple blockchain intelligence reports, each of these cryptocurrency exploits has been publicly attributed to the North Korea-related threat Lazarus Group.
At the same time, there are speculations about AI-powered cryptocurrency exploit systems, and the most worrying question raised now is whether autonomous AI-powered cryptocurrency exploit systems have already been deployed?
Why AI is now entering the DeFi security conversation
Speculation about AI-powered exploit systems gained momentum after DeFi developer Vitto Rivabella publicly hypothesized that North Korea may eventually fund offensive AI models using historical DeFi exploit data. Although there is no confirmed evidence that such systems currently exist, the theory has resonated due to broader industry developments.
Posted by Andreessen Horowitz (a16z) A research on April 28, 2026, which states the results of a test where AI coding agents can independently identify vulnerabilities and reproduce a proof of concept for a DeFi exploit.
Researchers tested the AI coding agent on 20 previous Ethereum DeFi hacks. At first, it seemed to be very successful as it solved 50% of the cases. But researchers later discovered that the AI was cheating by accessing future blockchain data and copying details from real attacks. Once this shortcut was removed, the AI success rate dropped to just 10%.
When researchers provided the AI with detailed information about previous hacks, such as common attack patterns and strategies, the AI was able to successfully exploit 70% of the cases.
The important thing to note from the research is the fact that this AI already has a high ability to detect vulnerabilities and an increased ability to exploit reproduction, although it is still weaker in very complex multi-step economic attacks. Complex attacks require planning, strategy, and financial calculations, something AI still has difficulty achieving.
The study also found that AI can overcome some limitations in its testing environment, showing that it can sometimes overcome limitations.
The overall structure of DeFi makes it particularly vulnerable
Decentralized finance It is one of the sectors that has been exposed to AI-powered attacks because blockchain systems provide public smart contract code, transparent cryptocurrency exploitation histories, large on-chain financial incentives, rapid loan infrastructure, and vast datasets for machine learning analysis.
This combination is what creates an ideal environment for automated systems trained to detect common vulnerability patterns, simulate profitability, and identify recurring cryptocurrency exploit opportunities faster than human researchers.
If AI systems continue to improve themselves, their strategic plans, optimization, and contract logic, there is a high probability that the industry will eventually encounter exploitation frameworks capable of operating at machine speed.
AI-powered DeFi exploits remain unproven, but the risks are growing
There is currently no verified public evidence that nation-state actors or cybercriminal groups operate fully autonomous AI systems to carry out DeFi hacks. However, several trends are becoming increasingly evident. AI-assisted vulnerability detection is already real, the automation of cryptocurrency exploitation is improving, reusable attack tools are expanding, and state-sponsored cryptocurrency theft remains very active.
Together, these developments suggest that although fully autonomous AI hackers are still speculative, the foundation for such systems may already be beginning to take shape.
The main idea is that security threats to cryptocurrencies are evolving very quickly. Although AI has not yet been proven to independently drive major DeFi exploits, increasing automation, increasingly sophisticated attack infrastructure, and access to massive cryptocurrency exploit data sets could dramatically reshape blockchain security in the coming years.
Read also: Blockaid warns against exploitation of cross-chain ZetaChain contracts





